 VoIP technology has clear advantages over traditional circuit switched telephony. One of the most prominent advantages of Hosted VoIP is its relative affordability as call volume scales up. We call it “price-performance”. Unfortunately ethical and legal business operators are not the only ones to take advantage of this benefit. Accessibility of hosted VoIP resulted in lowering the cost of predictive dialing (technology allowing a PBX system to place many calls automatically).
VoIP technology has clear advantages over traditional circuit switched telephony. One of the most prominent advantages of Hosted VoIP is its relative affordability as call volume scales up. We call it “price-performance”. Unfortunately ethical and legal business operators are not the only ones to take advantage of this benefit. Accessibility of hosted VoIP resulted in lowering the cost of predictive dialing (technology allowing a PBX system to place many calls automatically).
This spam takes interactive and non-interactive forms. By interactive I mean any unsolicited robotic calls that let you talk to a live agent. Non-interactive spam is typically presented as message broadcasts (be they text, voice or email).
Filtering voice spam is technologically far more difficult than filtering email. When we filter our email, in addition to blocking source address or phone number, we also use adaptive heuristic filters that look for text patterns. These filters are engaged prior to email or text reaching your mailbox. But voice calls take place in real time and it is a bit pointless to filter a phone call after you already picked up handset’s receiver. Another quality of VoIP protocols that are commonly used by many Hosted PBX service providers is that SIP (Session Initiation Protocol) makes it extremely easy to “spoof” calls. Calls can be placed by a program that can be very easily adopted to send randomized caller ids to the public switched network. This powerful feature makes VoIP phones extremely portable and allows VoIP PBXes to be quickly reconfigured to supply appropriate E911 information for each extension. It also makes it possible to write an unsophisticated program to produce a different and seemingly random caller id for each call that would be difficult or impossible to track. This caller-id “spoofing” renders any source number blocking pretty useless because the next call may come from a completely different number.
If developing software that produces mass calls is a fairly unsophisticated task, developing defense algorithm against voice spam is a costly and complex undertaking which involves algorithmic science and engineering. In March of 2007, ACM Transactions on Autonomous and Adaptive Systems published a paper by PRAKASH KOLAN and RAM DANTU of the University of North Texas called “Socio-Technical Defense against Voice Spamming”. While this paper is clearly a sample of scientific research, one does not have to be a scientist to realize that any algorithmic approach to the problem is prone to have undesirable false positives. Would you rather block an important call as a false positive or would you deal with the spam in lieu of not missing it? I am afraid that there is no clear-cut answer to that question because importance is relative just as our ability to tolerate interruptions by SPIT at any given moment.
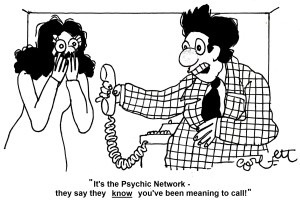
By itself, Spamming over Internet Telephony is not the most dangerous VoIP security threat. But it can aid in phishing over VoIP where a voicemail is left from a seemingly trusted source usually asking for privileged or confidential information.
Defense Options
As with everything else, when it comes to defense our options are weighed by effectiveness vs. cost of implementation. I will attempt to sort them in the order of cost-effectiveness.
-
- Do Not Call List is most likely the least expensive and the most effective defense against SPIT. Unfortunately it comes with its many limitations. First, since this is a U.S. based list with limited jurisdiction. It does not limit calls from or on behalf of political organizations, charities and telephone surveyors. In the United States, National Do Not Call Registry does not apply to Business-to-Business calls or calls originating from outside of the U.S. borders. With the cost of International calling plummeting due to spread of VoIP technologies, the number of off-shore “spamvertising” call centers targeting U.S. telephone numbers, have increased drastically over the past decade.
-
- Whitelisting is a technique often used in email. It allows calls only from the phone numbers explicitly specified in your list. While this technique is highly effective it also prevents legitimate new callers from reaching the destination. This technique is hardly suitable for 99% of operating businesses
-
- Blacklisting is an opposite to Whitelisting. Black list is a list of numbers, calls from which are to be blocked. Primary shortcoming from this technique is that it is extremely easy to circumvent by sourcing many different caller-ids. Also, some callers may use proxy dialing where a third party calls two numbers and then bridges the call.
-
- Reputation Filtering offer access to sophisticated algorithms which are used to calculate scores for phone numbers from which calls are originated. Such filtering can be based on a accessing a database containing such scores or calculating its score dynamically. Unfortunately, such calculation takes place while call is being has already reached its intended recipient destination and it may often prohibitively delay answer. These algorithms can be effective but they are also costly to implement and have high potential of being circumvented.
- Caller Screening requires a caller to record a short voice message which will be listened to by the recipient prior to him accepting a call. This technique does not do anything for voicemail spam but it can be very effective in reducing the duration of unwanted calls. Caller screening can be made practical and effective when combined with the whitelisting.
Of all of the above mentioned techniques, I believe that combining caller screening with whitelists and blacklists are the most cost-effective and practical solutions to reducing business VoIP spam. That is why we are strongly considering adding it to the DLS Hosted PBX product roadmap.